26 December 2024, Thu |
1:50 PM

Kaspersky researchers discovered a poorly detected SessionManager backdoor that was installed as a malicious module within Microsoft’s Internet Information Services (IIS), a popular web server.
Once installed, SessionManager allows for a wide range of malicious activities, from email collection to complete control over the victim’s infrastructure.
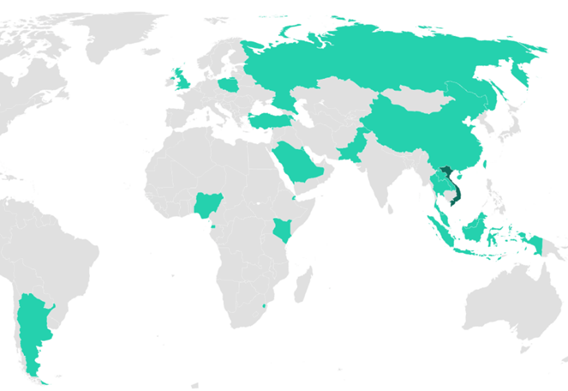
The newly discovered backdoor, which was first used in late March 2021, has affected governmental institutions and non-governmental organizations all over the world, with victims in eight countries from the Middle East, Turkey, and Africa region, including Kuwait, Saudi Arabia, Nigeria, Kenya, and Turkey.
Kaspersky discovered “Owowa” in December 2021, a previously unknown IIS module that steals credentials entered by a user when logging into Outlook Web Access (OWA). Since then, the company’s experts have kept a close eye on the new avenue for cybercriminal activity – it has become clear that deploying a backdoor within IIS is a trend for threat actors who previously exploited one of the “ProxyLogon-type” vulnerabilities within Microsoft Exchange servers. Kaspersky experts discovered a new unwanted module backdoor called SessionManager during a recent investigation.
“The exploitation of exchange server vulnerabilities has been a favorite of cybercriminals looking to get into targeted infrastructure since Q1 2021. It notably enabled a series of long unnoticed cyberespionage campaigns. The recently discovered SessionManager was poorly detected for a year. Facing massive and unprecedented server-side vulnerability exploitation, most cybersecurity actors were busy investigating and responding to the first identified offences. As a result, it is still possible to discover related malicious activities months or years later, and this will probably be the case for a long time,” comments Pierre Delcher, Senior Security Researcher at Kaspersky’s Global Research and Analysis team.
“Gaining visibility into actual and recent cyberthreats is paramount for companies to protect their assets. Such attacks may result in significant financial or reputational losses and may disrupt a target’s operations. Threat intelligence is the only component that can enable reliable and timely anticipation of such threats. In the case of Exchange servers, we cannot stress it enough: the past-year’s vulnerabilities have made them perfect targets, whatever the malicious intent, so they should be carefully audited and monitored for hidden implants, if they were not already,” adds Pierre.
The SessionManager backdoor allows threat actors to maintain persistent, update-resistant, and rather stealth access to a targeted organization’s IT infrastructure. Once inside the victim’s system, cybercriminals can gain access to company emails, update further malicious access by installing other types of malware, or secretly manage compromised servers that can be used as malicious infrastructure.
SessionManager’s low detection rate is one of its distinguishing features. Some of the backdoor samples, discovered by Kaspersky researchers in early 2022, were still not flagged as malicious by most popular online file scanning services. According to a Kaspersky Internet scan, SessionManager is still used in more than 90% of targeted organizations.
SessionManager compromised 34 servers across 24 organizations in Europe, the Middle East, South Asia, and Africa. The threat actor behind SessionManager is particularly interested in NGOs and government entities, but medical organizations, oil companies, and transportation companies, among others, have also been targeted.
Because of the similar victimology and use of the common “OwlProxy” variant, Kaspersky experts believe the malicious IIS module was used as part of the GELSEMIUM threat actor’s espionage operations.
Kaspersky products detect several malicious IIS modules, including SessionManager.
To protect your businesses from such threats, Kaspersky experts also recommend that you:
• Regularly check loaded IIS modules on exposed IIS servers (notably Exchange servers), leveraging existing tools from the IIS servers suite. Check for such modules as part of your threat hunting activities every time a major vulnerability is announced on Microsoft server products.
• Focus your defense strategy on detecting lateral movements and data exfiltration to the internet. Pay special attention to outgoing traffic to detect cybercriminal connections. Back up data regularly. Make sure you can quickly access it in an emergency.
• Use solutions like Kaspersky Endpoint Detection and Response and the Kaspersky Managed Detection and Response service, which help to identify and stop the attack in the early stages, before the attackers achieve their goals.
• Use a reliable endpoint security solution, such as Kaspersky Endpoint Security for Business (KESB), that is powered by exploit prevention, behavior detection and a remediation engine that is able to roll back malicious actions. KESB also has self-defense mechanisms that can prevent its removal by cybercriminals.