23 December 2024, Mon |
2:17 AM

Kaspersky researchers discovered an unusual malicious bundle (a collection of malicious programs distributed in the form of a single installation file, self-extracting archive, or other file with installer-type functionality) targeting gamers on YouTube. Its main payload is the widely used RedLine stealer, one of the most common Trojans used to steal passwords and credentials from browsers.
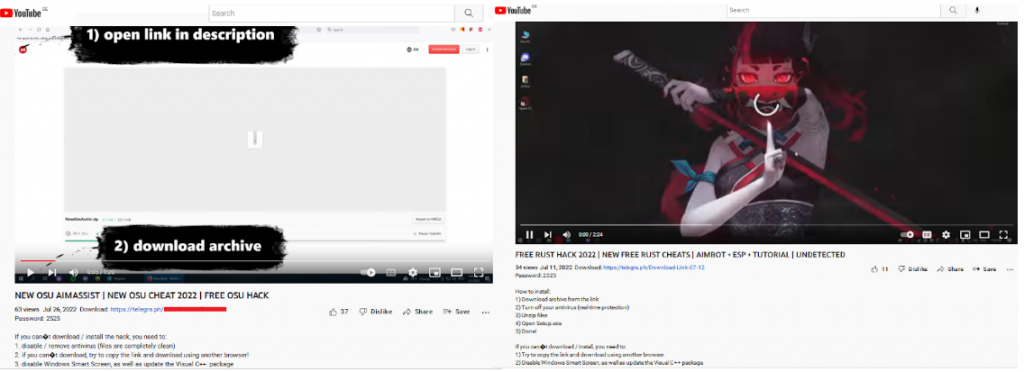
Criminals are always looking for gaming accounts and gaming computer resources. According to Kaspersky experts in a recent overview of gaming-related cyberthreats, stealer-type malware is frequently distributed under the guise of game hacks, cheats, and cracks. This time, the researchers discovered a new type of malicious activity associated with gaming: the attackers posted poisoned bundles disguised as gaming-related content on the victims’ YouTube channels, with a link to a self-extracting RAR archive in the video description. A well-known RedLine stealer is among the malicious files in the archive.
The stealer can plunder usernames, passwords, cookies, bank card details and autofill data from Chromium- and Gecko-based browsers, data from cryptowallets, instant messengers and FTP/SSH/VPN clients, as well as files with particular extensions from devices. In addition, RedLine can download and run third-party programs, execute commands in cmd.exe and open links in the default browser. The stealer spreads in various ways, including through malicious spam e-mails and third-party loaders.
In addition to the RedLine payload itself, the discovered bundle is of note for its ability for self-propagation. Several files, in the bundle in the description, are responsible for this. They receive videos and post them to the infected users’ YouTube channels along with the links to a password-protected archive. The videos advertise cheats and cracks and provide instructions on hacking popular games and software. Among the games mentioned are APB Reloaded, CrossFire, DayZ, Dying Light 2, F1® 22, Farming Simulator, Farthest Frontier, FIFA 22, Final Fantasy XIV, Forza, Lego Star Wars, Osu!, Point Blank, Project Zomboid, Rust, Sniper Elite, Spider-Man, Stray, Thymesia, VRChat and Walken.
Once the victims themselves download the original bundle, the RAR archive is self-extracting. It contains a number of malicious files, clean utilities and a script to automatically run the unpacked contents. Some of the files’ names include explicit language.
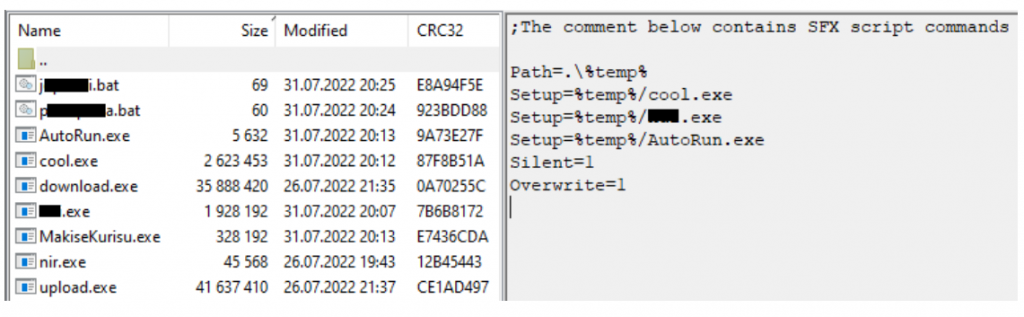
Another element that caught the researchers’ eye, is a miner. It makes sense, since the main target audience, judging by the video, is gamers. — They are likely to have video cards installed that can be used for mining.
“Gamers are one of the most popular groups targeted by cybercriminals. This time attackers used gaming related content as bait for stealing victims’ credentials as well as mining from their computers. Our advice would be to carefully pick the sources to quench your gaming thirst and do not download any suspicious archives from unreliable accounts,” comments Oleg Kupreev, senior security researcher at Kaspersky.
To protect yourself from malware hidden in open-source packages, Kaspersky recommends the following: