
Fortinet has released the latest semiannual FortiGuard Labs Global Threat Landscape Report.
According to the report, the second half of 2021 observed a rise in the automation and speed of attacks, revealing more advanced persistent cybercrime techniques that are more disruptive and unexpected.
Furthermore, cyber attackers are aiming to exploit the growing attack surface of hybrid employees and hybrid IT.
Derek Manky, Chief, Security Insights & Global Threat Alliances, FortiGuard Labs says: “Cybersecurity is a fast-moving and dynamic industry, but recent threat events show unparalleled speeds at which cyber adversaries are developing and executing attacks today. New and evolving attack techniques span the entire kill chain but especially in the weaponization phase, showing an evolution to a more advanced persistent cybercrime strategy that is more destructive and unpredictable.”
“To protect against this broad scope of threats, organizations need to implement AI-powered prevention, detection, and response strategies based on a cybersecurity mesh architecture allowing for much tighter integration, increased automation, as well as a more rapid, coordinated, and effective response to threats across the extended network,” Manky added.
The highlights of the 2H 2021 report are as follows:
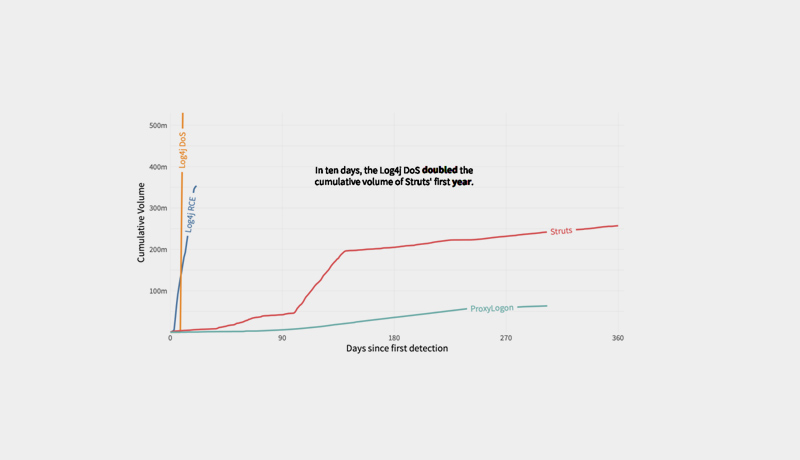
Log4j Demonstrates Dramatic Speed of Exploit Organizations Face: The Log4j vulnerabilities that occurred in late 2021 demonstrate the rapidly increasing speed of exploit that cybercriminals are attempting to leverage to their advantage. Despite emerging in the second week of December, exploitation activity escalated quickly enough, in less than a month, to make it the most prevalent IPS detection of the entire second half of 2021. In addition, Log4j had nearly 50x the activity volume in comparison to the well-known outbreak, ProxyLogon, that happened earlier in 2021. The reality is that organizations have very little time to react or patch today given the speeds that cyber adversaries are employing to maximize fresh opportunities. Organizations need AI and ML-powered intrusion prevention systems (IPS), aggressive patch management strategies, and threat intelligence visibility to prioritize those threats propagating most quickly in the wild to reduce overall risk.
Adversaries Rapidly Targeting New Vectors Across the Attack Surface: Some lesser or low-lying threats have the potential to cause bigger problems in the future and are worthy of watching. An example is newly crafted malware designed to exploit Linux systems, often in the form of executable and linkable format (ELF) binaries. Linux runs the back-end systems of many networks and container-based solutions for IoT devices and mission-critical applications, and it is becoming a more popular target for attackers. In fact, the rate of new Linux malware signatures in Q4 quadrupled that of Q1 2021 with ELF variant Muhstik, RedXOR malware, and even Log4j being examples of threats targeting Linux. The prevalence of ELF and other Linux malware detections doubled during 2021. This growth in variants and volume suggests that Linux malware is increasingly part of adversaries’ arsenal. Linux needs to be secured, monitored and managed like any other endpoint in the network with advanced and automated endpoint protection, detection and response. In addition, security hygiene should be prioritized to provide active threat protection for systems that may be affected by low-lying threats.
Botnet Trends Show a More Sophisticated Evolution of Attack Methods: Threat trends demonstrate that botnets are evolving to adopt newer and more evolved cybercriminal attack techniques. Botnets are no longer largely monolithic and focused solely on DDoS assaults; instead, they are multifunctional attack vehicles that employ a number of more complex attack strategies, including ransomware. Organizations must implement zero trust access solutions to provide the least amount of access privileges, particularly to secure IoT endpoints and devices entering the network, as well as automated detection and response capabilities to monitor anomalous behaviour, in order to protect networks and applications.
Malware Trends Show Cybercriminals Maximizing “Remote Everything:” Evaluating the prevalence of malware variants by area suggests that cyber adversaries continue to be interested in optimising the remote work and learning attack vector. With hybrid work and learning still a possibility, there are fewer levels of defence between malware and potential victims. Organizations must embrace a “work-from-anywhere” approach to security by installing technologies that can track, enable, and protect people no matter where they are. They require enhanced endpoint security (EDR) in conjunction with zero trust access solutions, such as ZTNA. Secure SD-WAN is also essential for ensuring secure WAN connectivity over the extended network.
Ransomware Activity Still High and Continues to Get More Destructive: According to FortiGuard Labs research, ransomware has not decreased from high levels over the previous year, but rather, the sophistication, aggression, and effect of ransomware is growing. Threat actors continue to target companies with a wide range of new and previously observed ransomware strains, frequently leaving a path of damage in their wake. Old ransomware is actively updated and improved, often with wiper software added, while new ransomware is emerging to use Ransomware-as-a-Service (RaaS) revenue models. RaaS allows more threat actors to use and disseminate malware without having to write it themselves.
Deeper Understanding of Attack Techniques Can Help Stop Criminals Faster: FortiGuard Labs investigated the functionality of identified malware by detonating malware samples gathered throughout the year to observe the destructive effects of various attacks. The end result was a list of specific tactics, methods, and procedures (TTPs) that the malware would have carried out if the attack payloads had been implemented. This high-resolution information demonstrates that detecting an adversary sooner is more important than ever, and that by focusing on a few of the discovered strategies, an organisation may successfully shut down a malware’s assault methods in some instances.

Protecting Against Fast-moving and Sophisticated Cyber Adversaries: Securing against evolving attack techniques will require smarter solutions that know how to ingest real-time threat intelligence, detect threat patterns and fingerprints, correlate massive amounts of data to detect anomalies, and automatically initiate a coordinated response. Point products need to be replaced with a cybersecurity mesh platform that provides centralized management, automation and integrated solutions that work in concert.