
Check Point Research (CPR) investigated OpenSea, the world’s largest NFT marketplace and the Check Point Software found critical security flaws and stops theft in OpenSea. If it was left unpatched, the vulnerabilities could allow hackers to hijack user accounts and steal entire cryptocurrency wallets by crafting malicious NFTs.
OpenSea is known as the world’s largest NFT marketplace, recording US$3.4 billion in transaction volume in August 2021 alone.
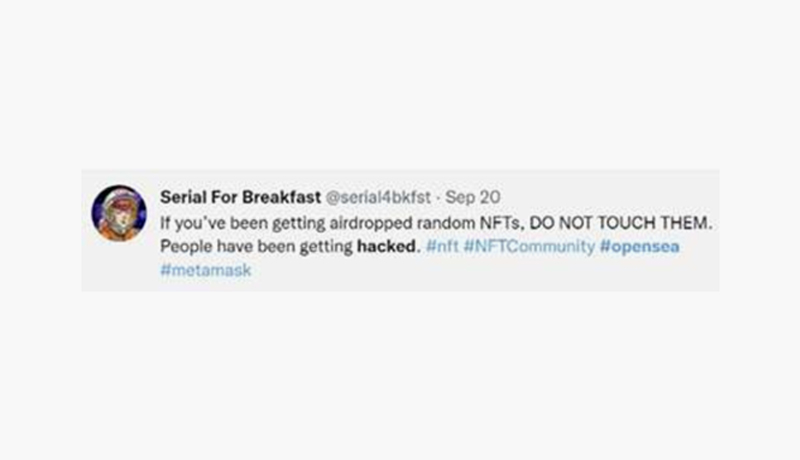
The CPR probe into OpenSea was spurred by reports of customers receiving free airdropped NFTs. Curiosity led CPR to contact a victim of a stolen crypto wallet, who acknowledged engaging with an airdropped object previous to the theft of their account.
Figure 1. Tweet warning of hacks related to airdropped NFTs
CPR discovered serious security issues in OpenSea, demonstrating how a malicious NFT might be leveraged to steal crypto wallets and hijack accounts. The following actions would have been necessary for successful exploitation of the vulnerabilities:
On Sunday, September 26, 2021, CPR promptly and properly informed OpenSea of its findings. OpenSea corrected the problem and validated it in less than an hour after it was discovered. To ensure that the fix functioned properly, CPR worked closely and collaboratively with the OpenSea team. OpenSea was quick to respond and released svg files containing iframe objects from their storage domain, allowing CPR to examine and close all attack paths simultaneously.
When getting requests to sign your wallet online, CPR advises caution. Before you approve a request, carefully analyse what is being sought and determine whether it is unusual or questionable. If you have any misgivings, you should refuse the request and investigate further before granting such permission.
Oded Vanunu, Head of Products Vulnerabilities Research at Check Point Software, said: “Our interest in OpenSea sparked when we saw chatter of stolen crypto wallets online. We speculated that an attack method existed in the wild around OpenSea, so we initiated a thorough investigation of OpenSea’s platform. The result was the discovery of a way to steal crypto wallets of users, simply by sending a malicious NFT through OpenSea. We immediately and responsibly disclosed our findings to OpenSea, who quickly worked with us to deploy a fix. I believe that our research findings, and the quick action by OpenSea, will prevent thefts of crypto wallets of users. Blockchain innovation is fast-underway and NFTs are here to stay. Given the sheer pace of innovation, there is an inherent challenge in securely integrating software applications and crypto markets. Bad actors know they have an open window right now to take advantage of, with consumer adoption spiking, while security measures in this space still need to catch up. The cyber security community must step up to help pioneering blockchain technologies secure crypto assets of consumers. We sternly warn the OpenSea community to watch out for suspicious activity that may lead to theft, as we believe bad actors will continue to expand their efforts, in order to hijack crypto wallets while exploiting system vulnerabilities.”
Statement from OpenSea: “Security is fundamental to OpenSea. We appreciate the CPR team bringing this vulnerability to our attention and collaborating with us as we investigated the matter and implemented a fix within an hour of it being brought to our attention. These attacks would have relied on users approving malicious activity through a third-party wallet provider by connecting their wallet and providing a signature for the malicious transaction. We have been unable to identify any instances where this vulnerability was exploited but are coordinating directly with third-party wallets that integrate with our platform on how to help users better identify malicious signature requests, as well as other initiatives to help users thwart scams and phishing attacks with greater efficacy. We are also doubling down on community education around security best practices and have kicked off a blog series on how to stay safe on the decentralized web. We encourage new users and seasoned veterans alike to give the series a read. Our goal is to empower the community to detect, mitigate and report attacks in the blockchain ecosystem, such as the one demonstrated by CPR.”
